- VMware Technology Network
- :
- Digital Workspace
- :
- Workspace ONE
- :
- Workspace ONE Discussions
- :
- workplace one for Android SSO
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello , I am now setting up the workplace one for Android SSO.
I follow the Quick guide on vmware (http://pubs.vmware.com/workspace_one_aw-91/topic/com.vmware.ICbase/PDF/workspace_one_qs_guide.pdf)
but have some question about it
May any one can help me?
1). In the guide , section Android SSO step 3b.
What should I enter on the proxy? is it cert-proxy.vmwareidentity.com:443 or any others?
2). in step 5. what is the CA’s root and intermediate certificates?
is it the same which used by iOS SSO , that find in Groups & Settings > All Settings > System > Enterprise Integration > VMware Identity Manager?
3). i did not enable the OCSP or CRL , will it case any problem?
Thanks very much
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
problem fixed,
The HTTPS proxy should be set to certproxy.vmwareidentity.asia:5262
Maybe the region need to match the Worksapce one tenant.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
problem fixed,
The HTTPS proxy should be set to certproxy.vmwareidentity.asia:5262
Maybe the region need to match the Worksapce one tenant.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you have to do anything else to get this working properly? I've tried cert-proxy.vmwareidentity.com:443 and also certproxy.vmwareidentity.com:5262 in the proxy (I am in the US) and I am still getting access denied on the android devices. Looks like the tunnel application is launching properly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ,
Which certificate you upload in the Workspace one ?
Is it the Tunnel cert?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I used the same cert from the identity manager integration that I used for IOS. Do I need to change to one of the tunnel certs?
edit: just tried the cert from aw tunnel root with same problem
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
for my case , I am not using public certificate
I use Airwatch certificate .
And Android is not same as iOS , Android need to import the tunnel certificate which form setting > system > Enterprise Integration > VMware Tunnel > Configuration > Advance > Root Certificate
export the Certificate and upload in to workspace one > Identity & Access Management > Authentication Methods > Mobile SSO (for Android) > Root and intermediate CA certificates
I hope it can help you.
PS : This worksapce one is not easy to get information from internet for configure , and the official document cannot provide enough information for setup.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, I am also using AirWatch certificates. I tried with that Cert but am getting the same issue. Are you using the full AirWatch tunnel with the appliance deployed or did you enter a dummy hostname like they specified in the quick configuration guide?
It is frustrating that the documentation is incomplete and contradictory (for example, the Identity Manager config guide mentions using certproxy.vmwareidentity.com:5262 where the Quick Config guide says to use cert-proxy.vmwareidentity.com:443)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't have install or deploy the tunnel server/appliance
and for the hostname i just enter a fake domain in it.
so let me capture some screen and upload for you later.![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks,
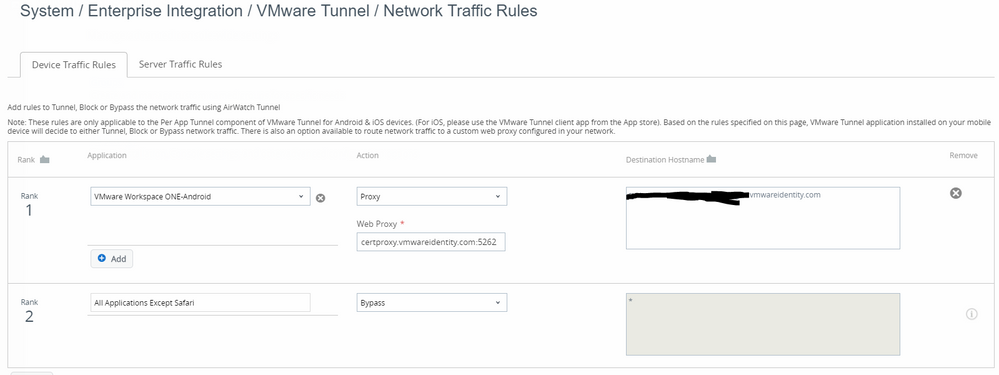
Here is my current config:
Cloud vIDM Access Policy added for Android Mobile SSO:
Mobile SSO Android Adapter enabled using root cert from the tunnel:
Mobile SSO for Android enabled on built-in auth adapter:
AW Tunnel Config:
Network Traffic Rules: (i also tried with cert-proxy.vmwareidentity.com:443) and also tried adding https:// in front of my destination hostname
Thanks for taking a look!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Look your configuration is similar with me.
In Workspace One

For the Android SSO , i don't select "Validate UPN Format" , but i am not sure is it the default setting.
The fallback is just added after i confirmed the SSO is working.
-----------------------------------------------------------------------------
In Airwatch
AW Tunnel Config:the hostname is not vaild ,just a fake hostname in our domain
and don't need to install the tunnel server .
Network Traffic Rules : after save , have you publish the rules?
The workspace one App : select the VPN profile and the AppServiceHost
And finally , please check the following :
1) have you deploy the vmware tunnel app to the Android device?
2) if you have deployed , open the vmware tunnel and see is it contain workspace one
click view profile
Finally , I find that if you have a access denied error , it may be the tunnel is not connected
if the tunnel is connected (The key icon on the left top corner) , any you see a error "Server error, please try again later" , it should be the HTTPS server problem.
hope can help you.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for taking the time to reply with all of that info. I confirmed my setup is the same as yours. Not sure what is going on . Gotta try to get ahold of someone at VMware.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Still haven't been able to get this working. Do you have a profile pushing a user certificate out to android devices?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
no user certificate profile.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
in the log "Connect to 10.160.5.55:5262 [/10.160.5.55] failed: connect timed out"
did you open the firewall port for it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it have done when i turn on certproxy on IDM and used proxy mode on traffic tunnel but when i use bypass mode, the problem appear. the firewall rule is open for 5262 two-way.
#YIPKC can you give me your contact (ex. Skype) to discuss about airwatch, it's ok ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't have skype, sorry
and i am still confuse for integration with airwatch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi vietnguyen2304,
We have exactly the same problem with SSO Android :
com.vmware.horizon.adapters.certproxy.exceptions.CertProxyClientException: org.springframework.web.client.ResourceAccessException: I/O error on GET request for "https://YY.YY.YY.YY:5262/clientData/42781": Connect to XX.XX.XX.XX:5262 [/YY.YY.YY.YY] failed: connect timed out; nested exception is org.apache.http.conn.ConnectTimeoutException: Connect to ZZ.ZZ.ZZ.ZZ:5262 [/WW.WW.WW.WW] failed: connect timed out....
Have you fixed it ?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi jnovelle
What's Your airwatch enviroment? i get the error on Andoird when i config bypass tunnel (on-premises) enviroment ! but when i change from bypass to proxy (IDM on-premises) it's work
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have vIDM on premise and Airwatch on SaaS.
The only difference is that we have the same FQDN for the certproxy (5262 port) and for vIDM access.